The hackers behind the ransomware encrypted files on the system, preventing the firm from having access to its own files. They then asked for $500,000 (450,000 euros) paid in Bitcoin to reverse the attack, engaging in cryptoviral extortion.
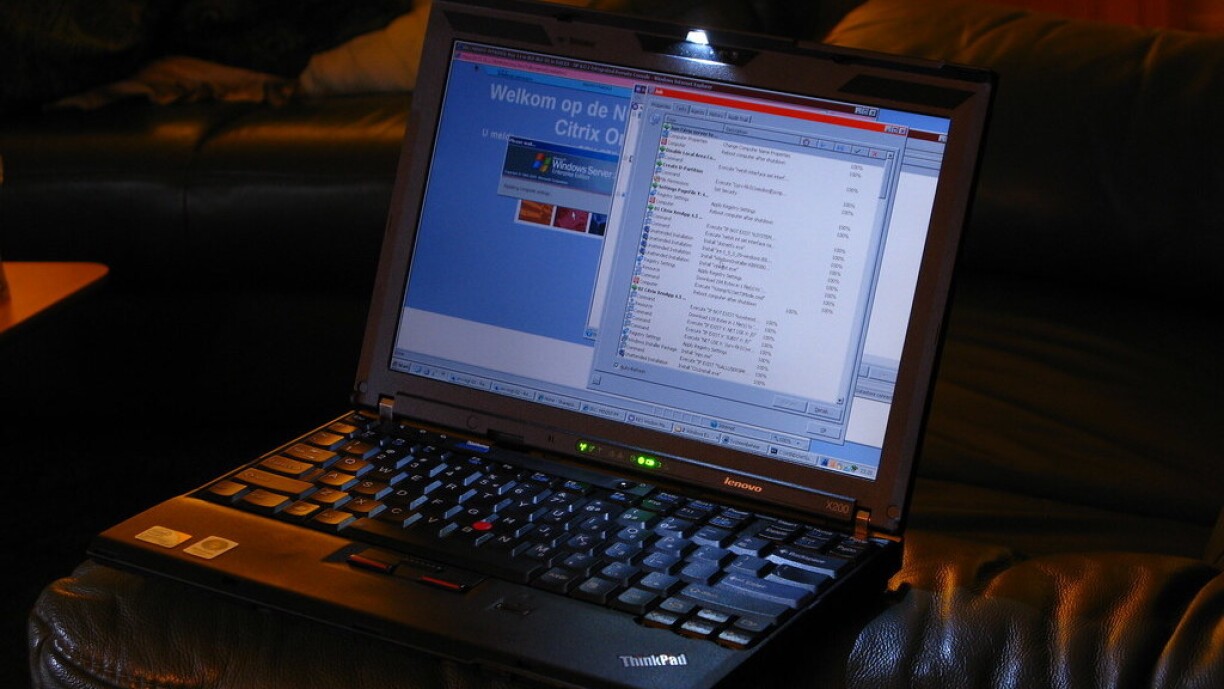
In December, hackers exploited a flaw in American firm Citrix's software. At the same time, the firm was working on a hardware issue.
Citrix clients throughout the world received a system update which had a bug in it. The bug then allowed hackers into the system. The Luxembourgish firm's case was not unique, as Citrix system all over the globe were hacked.
The Luxembourgish construction firm was paralysed by the hack and could not work for some time. Some 150 people working at the office were no longer able to get into the system and were initially concerned that hackers had destroyed backups containing all of the company's data. After three days, they discovered that hackers had only located the first backup and caused damage to it.
Thankfully, the firm found a second backup, providing reassurance that they could build a new system, according to one of the firm's managers.
It took the firm a considerable amount of time to build the new system, with employees working day and night. The losses the ransomware attack caused the firm has been hard to determine, and they have not been able to calculate a definitive figure.
According to management, a number of employees were forced to stay at home, as they were unable to work during that period, this was was the largest hit to the company operations.
Following this, the firm was forced to replace all its IT devices: new computers, new printers, faxes, new badge readers, and more. This came at a substantial cost of €300,000.
The firm was fortunate that construction workers were on annual leave at the time, and were able to return to work after, thus significantly lowering the impact of personnel costs. However, the business was not insured against such an attack.
The key issue for the firm was that in being unable to carry out operative business, and consequently not being able to process invoices nor pay salaries, there was a significant impact on cashflow.
Rebuilding the new IT system took some time and was still only operating at 95% completion by Monday 2 March - more than six weeks after the ransomware attack.
While building the new system, IT teams were especially careful to set up two completely new networks.
One of these was an internal network without internet access and outward communication, which was a particularly difficult task.
During that time, the business raised the possibility of working with alternative methods and communicating differently, by using typewriters and faxes.
Finally, the second network, which has internet access, is geared towards communication with clients. The two networks are not connected.
A number of questions remain unresolved following this cyberattack in a time of digitalisation and autonomous IT systems. The Computer Incident Response Centre Luxembourg (CIRCL) is a government initiative which collects and reports security gaps in IT.
The CIRCL had already been warned about the flaw in Citrix systems back in December 2019. However, the response centre did not know which businesses used Citrix. Unable to contact individual businesses, the CIRCL forwarded the information on to providers, who, it transpires, failed to contact the construction firm.
The firm stressed that legislation and procedures currently in place are simply not equipped for such attacks, as users are asked to inform the CIRCL of any risks, but the exchange is not reciprocal.
The German online IT magazine Golem analysed the security flaw throughout the world and concluded that the incident demonstrates one thing in particular: cybersecurity remains in a very basic realm.
If the warning was sounded and firms reacted one month later, it would be clear that security would no longer play a significant roll. Data reporters in Germany found weak spots on more than 2,000 servers, including hospitals, administrations, municipal councils, banks, research centres and more.
On Tuesday, Tageblatt reported a cyberattack targeting the BGL, with around 50 bank accounts targeted.
Between 20 and 24 February an international cyberband stole around €5,000 from each account, targeting both private customers and businesses.
The reason for the relatively 'low' amount is that the bank's check-ups are stricter on higher amounts and wold have triggered a closer look.
The hackers used phishing methods to access the accounts and it is reported that the victims have all been compensated.